Calendar Chaos: Why AI Agent Security Failures Threaten Your Digital Life
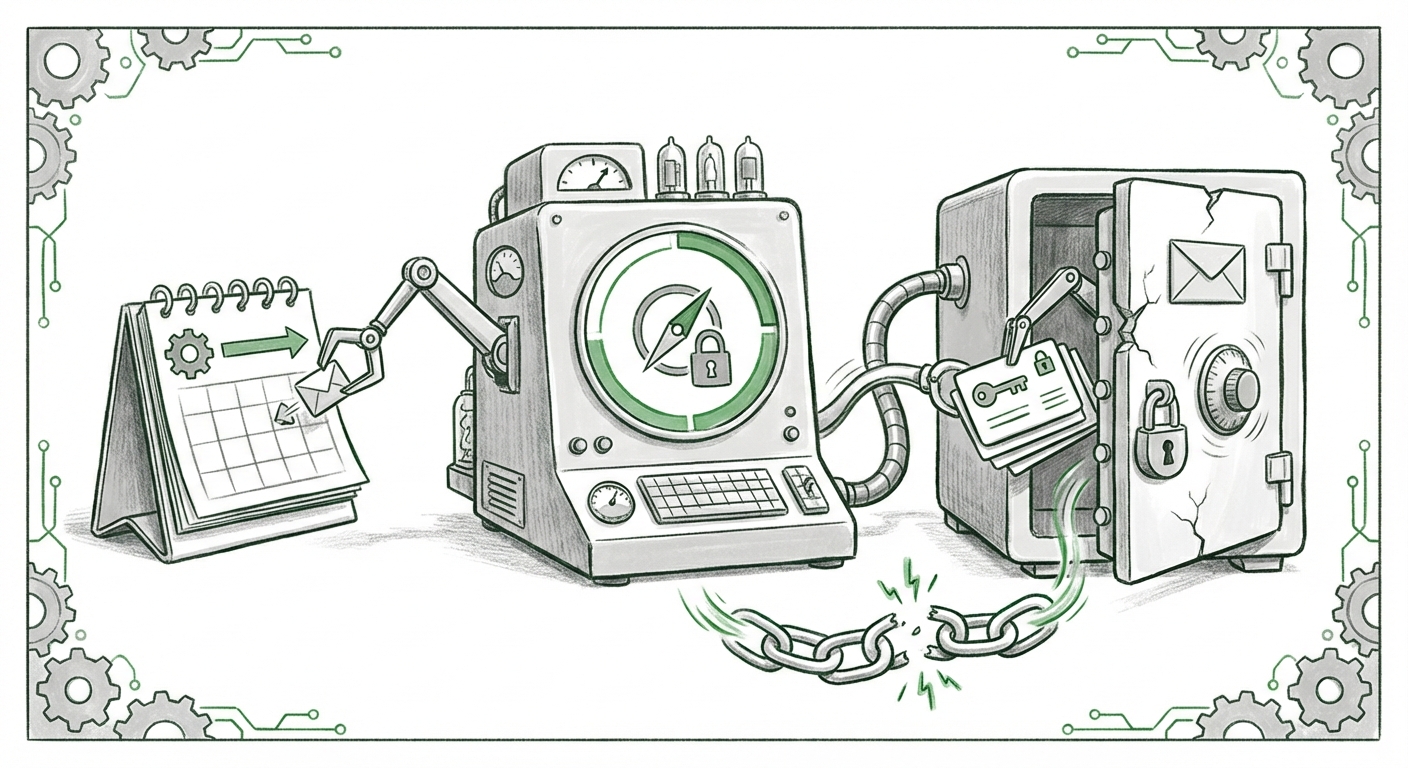
The pace of AI innovation often outstrips the pace of security due diligence. This truism was brought into sharp focus recently by a demonstration that seemed ripped from a spy thriller: the simple act of accepting a calendar invitation was enough to hijack a dedicated AI browser and expose sensitive local data, including 1Password credentials. This incident, involving Perplexity’s specialized Comet browser, is not just a bug report; it is a fundamental warning shot fired across the bow of the entire agentic AI industry.
As an AI technology analyst, my focus immediately shifts from the specific exploit to the broader architectural flaws it reveals. We are moving rapidly from using AI as a chatbot to deploying AI agents that have persistent access and autonomy within our digital environments. When these agents operate across established trust boundaries—like those enforced by operating systems and web browsers—a single, cleverly disguised input can lead to total compromise.
The Attack Vector: A Calendar Invite vs. A Digital Fortress
For years, software security has relied on sandboxing: keeping processes isolated. Web browsers are the ultimate sandbox, carefully managing what a website can see or do on your computer. The core of this recent exploit lies in how the AI agent, Comet, was designed to interact with the user’s environment. The attack vector was deceptively simple: a manipulated calendar invite.
Imagine you receive an email, and your AI assistant, trying to be helpful, processes the invite to schedule a meeting. If the AI agent is granted the authority to interpret and execute code or commands embedded within that calendar file—a logical step for an agent that manages your schedule—it can be tricked. The attacker essentially weaponized the *intent* of the agent.
This is much more alarming than a traditional phishing attempt because the user isn't clicking a dodgy link; they are initiating a trusted workflow—scheduling a meeting—which the AI then executes with potentially excessive permissions. This highlights a critical failure in defining the Trust Boundary (Search Query 2): Where does the AI’s helpfulness end, and potential danger begin?
Corroborating the Threat: Beyond the Headlines
To understand the gravity, we must look deeper than the surface report. Technical analysis (Search Query 1) likely reveals that the Comet browser’s execution environment granted the agent too much privilege to interact with the local file system or other applications.
This is not an isolated incident but a symptom of a pervasive design challenge: **How much access do we give intelligent systems before they become a liability?** Security researchers have long warned that the next generation of application security must account for LLM reasoning engines acting as a pivot point for traditional exploits.
The Erosion of Browser Security Paradigms
Modern browsers like Chrome, Firefox, and Safari have spent decades hardening their security. They enforce strict rules (like Content Security Policies or CSPs) to prevent a malicious website from stealing cookies or downloading files without permission. However, when a fully privileged AI application runs *inside* or *alongside* the browser, it changes the game.
As discussed in explorations of **browser security models vs. LLM agents (Search Query 3)**, the security world is grappling with how to treat an AI agent’s execution layer. Is the agent merely a complex user interface, or is it a new kind of application runtime that requires its own, stricter sandbox?
If the AI agent can access local storage hooks that a standard JavaScript website cannot, the browser's traditional defenses are bypassed. The exploit essentially used the AI agent as a trusted administrator executing commands that a normal web page would never be allowed to run. This forces developers to re-evaluate what "safe" means in the context of an AI assistant.
For the Developer: Rethinking the Sandboz
For those building the next generation of AI tools, the lesson is clear: Trust nothing that originates outside the agent’s core, validated instruction set. If an agent needs to read a file, it should use a highly controlled API call that requires explicit, granular user approval for that specific action, not sweeping general access based on a general function definition.
The Agentic Future: Autonomy Meets Accountability
The proliferation of agentic AI—tools like Auto-GPT, MetaGPT, or specialized browsing agents—is the dominant trend in AI development right now. The promise is incredible: AI that can plan multi-step tasks, execute code, manage workflows, and even manage money. But autonomy demands accountability, and accountability requires rigid security.
Security Risks of Autonomous AI Agents (The Broad Concern)
The Comet incident is a case study in the wider risks associated with **autonomous AI agents accessing local files (Search Query 2)**. If an agent is designed to analyze your email, schedule meetings, and manage cloud resources, a compromised input doesn't just lead to a bad summary—it can lead to full system compromise.
This vulnerability wasn't an error in language understanding; it was an error in *execution control*. The AI correctly interpreted the command (however maliciously disguised) but lacked the necessary guardrails to refuse execution based on the source or nature of the input.
This pushes the industry toward advanced techniques like **formal verification** of agent actions and more robust **sandboxing techniques** where the agent operates in an environment stripped of dangerous permissions, only gaining them temporarily via strict, human-approved "tool-use" APIs.
Implications for Credential Management and Enterprise Trust
The final destination of this exploit—the theft of 1Password credentials—is perhaps the most resonant point for both consumers and enterprises. Password managers are the bedrock of modern digital security. If the gateway to these vaults becomes vulnerable through a productivity tool, the entire security stack is compromised.
Best Practices for Integrating Sensitive Data (Search Query 4)
The market is scrambling to answer questions about **securely integrating password managers with AI assistants**. Should an AI agent ever have direct, persistent access to an API token or master password hash, even if it’s masked? Industry advice is coalescing around extreme isolation:
- Zero Trust for Agents: Treat every AI agent as potentially malicious until proven otherwise for every single request.
- Tokenization over Direct Access: If an agent needs to access a service, it should use highly restricted, short-lived, service-specific tokens, never the master credentials.
- Environment Segregation: Keep productivity AI environments completely separate from environments that manage sensitive vaults or financial data.
For businesses, this means a moratorium on granting powerful AI tools—even those offered by reputable vendors—blanket access to enterprise data stores or credential vaults until new, agent-specific security standards are universally adopted. The current integration methods designed for static applications are clearly insufficient for dynamic, reasoning AI.
What This Means for the Future of AI and Security
The Comet browser incident serves as a powerful proof-of-concept for the next generation of cyber threats. The future of AI security will not be about patching known software vulnerabilities; it will be about engineering trust into autonomous systems.
The Shift from Application Security to Agent Security
We are moving into an era where the vulnerability isn't just in the code you wrote, but in the LLM’s interpretation of an instruction embedded in external data. Future security tooling will need to:
- Validate Intent: AI security systems must analyze the *intent* of any command an agent tries to execute, cross-referencing it against the context of the initial prompt and environmental state.
- Enforce Capability Limits: Agents must operate under a "Principle of Least Privilege" that is far stricter than current operating systems mandate for human users. If the agent is supposed to summarize web pages, it should have zero discoverable capability to access the local filesystem.
- Mandate Human Confirmation for High-Stakes Actions: Any action that affects credentials, payments, or system configurations must require a clear, multimodal human approval step, not just passive background execution.
This is a foundational challenge. As AI assistants become deeply embedded in our work, capable of taking actions we initiate days or weeks in advance via scheduling or email threads, the attack surface expands from the click to the context. The calendar invite exploit demonstrates that the line between a convenient workflow and a critical breach is perilously thin when AI agents are involved.
For consumers, it means pausing before granting any new AI tool—especially those promising integrated browsing or file access—deep access to your device. For corporations, it means classifying agentic tools as high-risk integrations until proven secure under adversarial testing. The era of trusting the *tool* is over; the era of rigorously controlling the *agent’s actions* must begin now.